In the past 10 years, the number of electronic components used in automobiles has grown at an alarming rate. In-vehicle networks are also increasingly being designed or deployed in automobiles to connect multiple systems such as infotainment, car-assisted driving and security systems, often requiring a shared high-bandwidth infrastructure. At the same time, the in-vehicle network and the devices connected to it need to be diagnosed and maintained through an external interface. With the increasing degree of car networking, cars are actually becoming "networks on wheels," and the security concerns of network infrastructure are increasing. This article refers to the address: http:// Although the possibility of an in-vehicle network being attacked is low, this does not mean that it will not happen. If there is enough time and resources, the hacker can launch a series of attacks and possibly spread such attacks to all vehicles. In other words, a well-planned cyberattack will have a very broad impact. This is why car manufacturers and the industry itself are taking steps to ensure the safety of connected cars. For the past 10 years, Ethernet has been the most popular and reliable network technology in the world, and has been successfully and safely deployed in a dynamic and ever-changing enterprise environment. Due to the high bandwidth, high cost performance, universality and inherent network security of Ethernet, its use in automobiles is rising. And Ethernet's proven security has played a more significant advantage in automotive applications. In addition, since the equipment and configuration of the in-vehicle network are known and foreseeable, identifying and protecting them from threats is a very delicate process. Basic principles of Ethernet Message authentication and encryption are key features to ensure that car Ethernet is capable of preventing network damage. It provides the first invincible line of defense against malicious attacks. However, this feature alone is not enough to fully secure the connected car. Ethernet uses a standard packet format that includes source and destination addresses, VLAN tagging, and frame verification, which provide the foundation for verification, isolation, and data integration. Furthermore, because the in-vehicle network design is precise and static, and has the characteristics of predictable traffic, it provides users with the opportunity to closely configure and constrain the network operation according to the design intent. For example, whether through static configuration or dynamic learning, Ethernet switches can use packet addresses for traffic isolation and filtering. VLANs can be used to isolate different types of traffic on a shared physical network, ensuring that devices can only communicate with other devices in the domain. For example, a configured VLAN can be used for infotainment, while a single VLAN can be configured for car-assisted driving while the other can be used for security, and an Ethernet switch can enforce network isolation between the two. Figure 1: The Ethernet frame header contains the target MAC address and source MAC address as its first two fields, and a cyclic redundancy check (CRC) for verifying packet integrity. In addition, it may include virtual local area network (VLAN) tags that define the systems and processes used by the bridge and switch to support VLANs. An Access Control List (ACL) can be used to define a precisely configured action-passing rule when a packet is forwarded, which defines which site can transmit traffic and where the traffic can go. When the specified traffic level is exceeded, Storm Control helps the switch monitor traffic levels and discard broadcast, multicast, and unknown unicast packets to protect the network from violating the offending site. At the same time, flow-based governance accurately defines and enforces bandwidth rules at each flow level, which protects the network from rogue software or error software. In addition, a wide range of data standards enable exception monitoring through software. Device verification Although each Ethernet packet contains the source MAC address, the MAC address may also be falsely reported. The widely implemented 802.1x standard is an option to verify device availability before entering the vehicle network. 802.1x defines a standardized method for transporting the Extensible Authentication Protocol (EAP) framework over wired or wireless LANs. This framework allows for the exchange and verification of security certificates before they are authorized to enter the network. EAP supports many authentication methods (such as EAP-PSK and EAP-TLS), each of which has its own set of authentication keys and certificates for device authentication. The strength of the verification varies depending on the method and certificate used, and can be pre-configured in a proprietary environment such as manufacturing or maintenance equipment. Figure 2: 802.1x defines a standardized method for transporting the Extensible Authentication Protocol (EAP) framework over wired or wireless LANs. This framework allows for the exchange and verification of security certificates before they are authorized to enter the network. data encryption Data encryption ensures that only authorized parties can access the encoded data. Many layers of the communication protocol stack, including the Ethernet layer, can be encrypted. The 802.11AE MAC Security Protocol (MACSec) standard uses the 802.1x standard for secure key exchange and provides MAC-level encryption and message authentication for Ethernet. However, because this method requires hardware support, which increases cost and power consumption, it is not supported by mainstream devices. Figure 3: The inherent security features of automotive Ethernet may be the key to eliminating car safety hazards. Although Ethernet has long been used as an IT network technology, it is undeniable that the application of this technology in the field of car networking is constantly being explored. As the central backbone, automotive Ethernet provides automotive manufacturers with the necessary tools to secure their network infrastructure. Even more gratifying is that Ethernet has begun to prove its value. About the Author Ben Gale is currently the Technical Director of Infrastructure and Networks at Broadcom, where he is responsible for network control stack services for Ethernet bridging and routing. He has worked in product development and deployment in a variety of industries, including automotive, and has over 20 years of expertise. In addition, he served as Vice President of the AVnu Automotive Certification Development team, which is responsible for developing specifications and test plans for the Automotive Ethernet and Audio-Bridge Bridging (AVB) standards. Prior to joining Broadcom, Ben Gale served as Director of Product Development at 3Com. He graduated from the University College of Wales, Aberystwyth with a bachelor's degree in microelectronics and computer science.
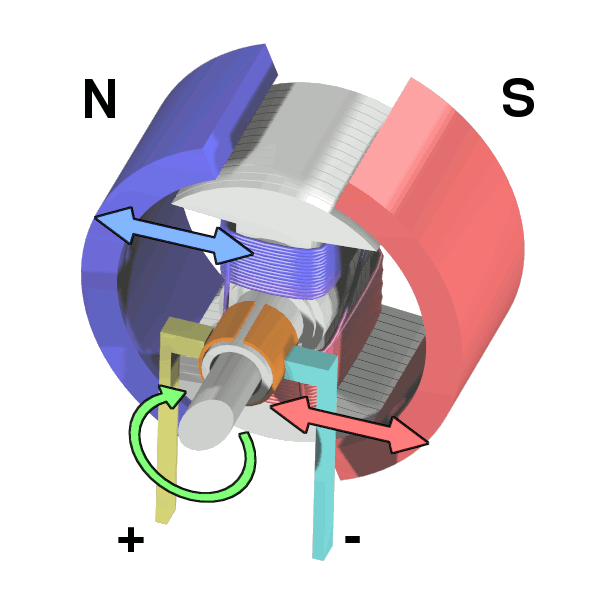
A DC motor is any of a class of rotary electrical
machines that converts direct current electrical energy into mechanical energy.
The most common types rely on the forces produced by magnetic fields. Nearly
all types of DC motors have some internal mechanism, either electromechanical
or electronic, to periodically change the direction of current flow in part of
the motor.
DC motors were the first type widely used, since they
could be powered from existing direct-current lighting power distribution
systems. A DC motor's speed can be controlled over a wide range, using either a
variable supply voltage or by changing the strength of current in its field
windings. Small DC motors are used in tools, toys, and appliances. The
universal motor can operate on direct current but is a lightweight motor used
for portable power tools and appliances. Larger DC motors are used in
propulsion of electric vehicles, elevator and hoists, or in drives for steel
rolling mills.
Dc motor areas of application: smart home field, robotics, precision medical equipment industry, automotive drive field, electronic products and personal care equipment
Application of the product:
Features: high torque, low noise, small volume, light weight, easy to use, running
constant speed, etc., can also be matched with various gearboxes to change the
output speed and torque.
Features: small volume, fast speed, stable performance, low price, good speed regulation.
Method
of use: the best stable in horizontal plane, installed on the dc motor output
shaft parts, cannot use a hammer to knock, knock prone to press into the dc
motor drive, may cause damage to internal components, and cannot be used in the
case of blocked.
Operating temperature range:
DC motor should be used at a temperature of -10~60℃.
The figures stated in the catalog specifications are based on use at
ordinary room temperature catalog specifications re based on use at
ordinary room temperature
(approximately20~25℃.
If a geared motor is used outside the prescribed temperature range,the
grease on the gearhead area will become unable to function normally and the
motor will become unable to start.Depending on the temperature conditions ,it
may be possible to deal with them by changing the grease of the motor's parts.Please feel free to consult
with us about this.
Storage temperature range:
DC motor should be stored ta a temperature of -15~65℃.
In case of storage outside this range,the grease on the gearhead area
will become unable to function normally and the motor will become unable to
start.
Service life:
â—Use with a
load that exceeds the rated torque
â—Frequent
starting
â—Momentary
reversals of turning direction
â—Impact
loads
â—Long-term
continuous operation
â—Forced
turning using the output shaft
â—Use in
which the permitted overhang load or the permitted thrust load is exceeded
â—A pulse
drive ,e.g.,a short break,counter electromotive force,PWM control
â—Use of a
voltage that is nonstandard as regards the rated voltage
â—Use
outside the prescribed temperature or relative-humidity range,or in a special
environment.
â—Please
consult with us about these or any other conditions of use that may apply,so
that we can be sure that you select the most appropriate model.
when it come to volume production,we're a
major player as well .each month,we rurn out
600000 units,all of which are compliant with the rohs directive.Have any
questions or special needed, please contact us, we have the engineer group and
best sales department to service to you Looking forward to your inquiry. Welcome to
our factory.
Dc Motor,Small Dc Motor,Mini Dc Motor,Robot Dc Motor,Dc Motor With Gearbox Shenzhen Shunchang Motor Co., LTD. , https://www.scgearmotor.com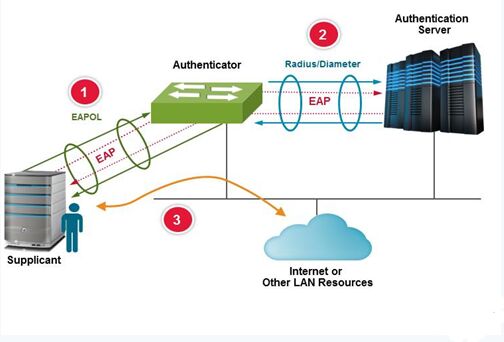






June 04, 2024