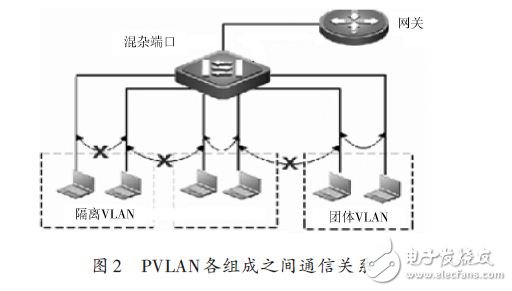
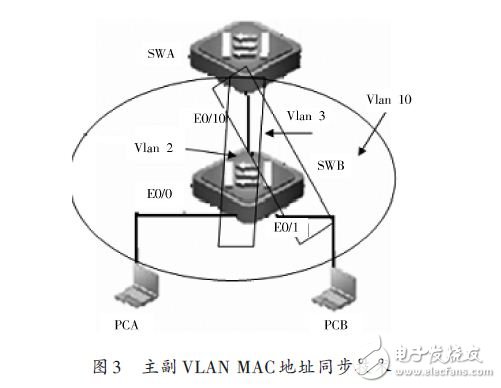
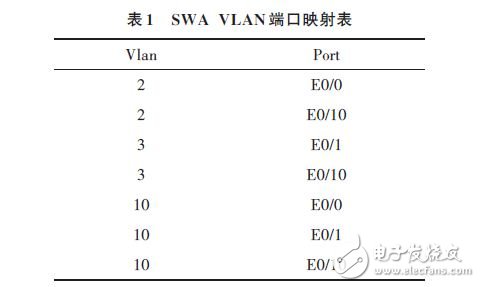
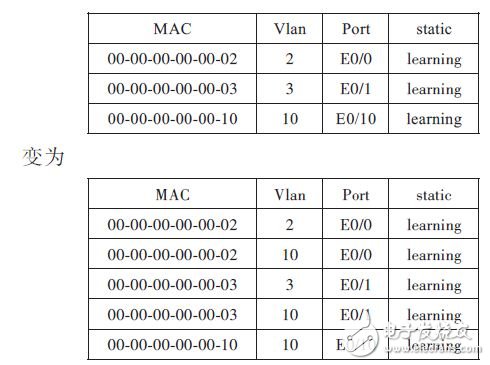
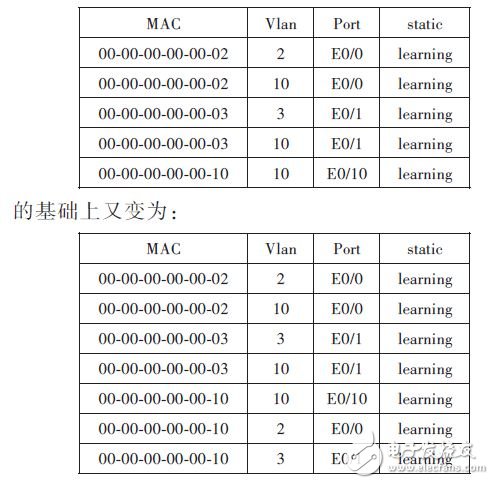
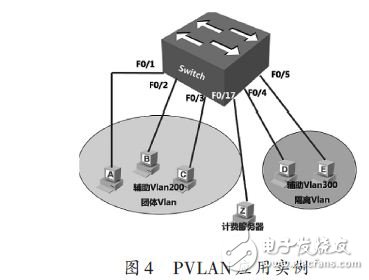
introduction With the rapid development of the network, the security requirements of network user communication are getting higher and higher; the traditional solution is to assign each customer a VLAN and related IP subnet. By using VLAN, each customer is from the second layer. Isolated, can prevent any malicious behavior and Ethernet information snooping. However, this model of assigning a single VLAN and IP subnet per customer creates the following limitations: the number of VLANs inherent in the switch; complex STP: For each VLAN, each associated Span? The topology of the ning tree needs to be managed; the IP address is in short supply: the division of the IP subnet is bound to cause waste of some IP addresses; the limitation of the route: each subnet needs the configuration of the corresponding default gateway. In order to solve the above problem, an advanced VLAN technology--private VLAN (Private VLAN) came into being. 1 PVLAN basic structure A private VLAN is a VLAN that can provide isolation for different ports in the same VLAN. A VLAN can divide a Layer 2 broadcast domain of a VLAN into multiple subdomains. Each subdomain consists of a pair of VLANs: Primary VLAN and Secondary VLAN, as shown in Figure 1. Primary VLAN: is the advanced VLAN of the PVLAN. There is only one primary VLAN in each PVLAN. Secondary VLAN: is a sub-VLAN in the PVLAN and is mapped to one primary VLAN. Each access device is connected to the secondary VLAN. The secondary VLAN has the following Two types: Isolated VLAN: Ports in the same isolated VLAN cannot communicate with each other through Layer 2, and only one isolated VLAN in a private VLAN domain. Community VLAN: A port in the same community VLAN can communicate at Layer 2, but cannot communicate with other ports in the community VLAN. A private VLAN can have multiple community VLANs. The communication relationship between the components of the PVLAN is shown in Figure 2. In the concept of Private VLAN, there are three switch port types: Isolated port: Is it an Isolated PVLAN, only with Promis? Cuous port communication, the Isolated port can not exchange traffic with each other; Community port: belongs to the Community PVLAN, can communicate with the Promiscuous port, can exchange traffic with each other; Promiscuous port: connected to the router or Layer 3 switch interface, the traffic it receives can be sent to Isolated port and Community port. The entire VLAN representing a Private VLAN is the Primary VLAN. The first two types of VLANs need to be bound to it, and it also includes the Promiscuous port. 2 PVLAN working mechanism The VLAN is dynamically learned according to the target MAC address, VLAN, and switch port to obtain this table for data exchange. The PVLAN uses two-layer VLAN isolation technology. Only the upper VLANs are visible globally, and the lower VLANs are isolated from each other. It is implemented by MAC address table synchronization technology between the primary VLAN and each secondary VLAN. As shown in Figure 3, set PVLAN, Vlan10 is the Primary VLAN, and the mapped Secondary VLAN is 2 and 3. The port configuration is shown in Figure 3. After this configuration, a Vlan will be formed inside the switch? For the port mapping entries, see Table 1. The MAC address synchronization technique has two steps: (1) The address learned by the secondary VLAN is synchronized to the primary VLAN, and the outbound interface is unchanged through this synchronization. At this time, the MAC address table of the SWB is: At this time, all the unicast data frames coming from the SWA know the explicit MAC address and the outgoing interface in the SWB, then the downlink unicast will not be unicast and broadcast, and the matching entries will be directly unicast. . 2) The address learned by the primary VLAN is synchronized to the secondary VLAN. The outgoing interface remains unchanged: At this point, as long as there is an exact SWA MAC address on the PCA, it pings the SWA again, and the packet has an explicit MAC address and outgoing interface on the SWB, so the uplink unicast will not be unicast and broadcast. In this way, regardless of whether the user's data is uplink or downlink, the data transmission avoids broadcasting as much as possible. 3 PVLAN application examples and configuration steps The application of PVLAN is very effective for ensuring the security of data communication of the access network, and the user only needs to connect with his own default gateway. A PVLAN does not require multiple VLANs and IP subnets to provide a connection with Layer 2 data communication security. All users access the PVLAN, which enables all users to connect to the default gateway without any access to other users in the PVLAN. The PVLAN function ensures that each port in the same VLAN cannot communicate with each other but can pass through a trunk port. This way, even users in the same VLAN will not be affected by the broadcast. Example application background: Requirement: Hosts A, B, and C are a group, they must be able to communicate with each other, and can communicate with the gateway and server Z, but cannot communicate with the rest of the hosts in the main Vlan 100; hosts D and E are a group between them. Can not communicate with each other, but can communicate with the gateway, billing server Z, and can not communicate with the rest of the host in the main Vlan 100; according to requirements, using PVLAN technology, the network topology can be designed as shown in Figure 4. The configuration steps are as follows: (1) Create each VLAN and declare the VLAN type; (2) Associate the primary VLAN with each secondary VLAN; (3) Divide ports for each VLAN; (4) Auxiliary VLAN mapping primary VLAN Layer 3 interface; (5) Set the IP address of each terminal and the IP address of the primary VLAN SVI interface. On one network segment, the default gateway is the IP address of the SVI interface. This achieves the isolation of different users in the same VLAN layer 2, and can only communicate with other users through the gateway, which enhances the security of the access network. MR FOG vape pen is portable and fashion disposable electronic cigarette, disposable ecigs pen are trending featured vape pen for vapors as it's safety and easy to use. Disposable vape pod,disposable vape, wholesale vape,vape wholesale,vape pen manufacturer and supplier.disposable vape pen,disposable electronic cigarette,disposable ecigs pen,disposable ecigs stick,disposable e-cigs pen,disposable vape factory,disposable vape pod,disposable vape device,vape pen,vape stick, vape wholesale,wholesale vape,customized dispsoable vape pen,customized vape pen,OEM&ODM disposable ecigs pen,disposable electronic cigarette wholesale, wholesale disposable electronic cigarette,distribute vape pen,vape pen distribute,high quality vape pen,high quality vape pod,rechargeable disposable vape pen,refillable vape pen,refilling electronic cigarette,rechargeable disposable electronic cigarette,refillable vape pod,disposable refillable ecigs,disposable refilling e-cigs pen,refillable e-cigs pen MR FOG vape ,disposable vape pen,vape wholesale, disposable electronic cigarette,ecigs pen Shenzhen Onlyrelx Technology Co.,Ltd , https://www.onlyrelxtech.com
April 25, 2024